OVERALL RATINGS
INSTALLS
196
SUPPORT
- Partner Supported
TRUST SIGNALS
Key highlights of the appAutomate software access requests and user access reviews in Okta, Entra ID, Google Workspace and Jumpcloud
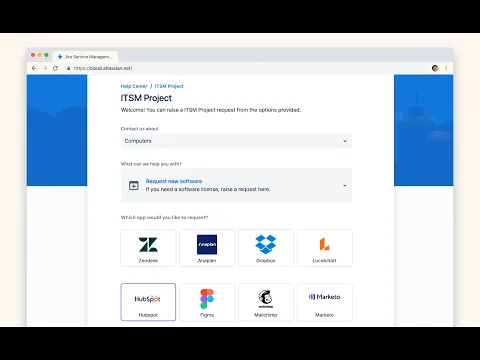
Streamline access requests with an app catalog
Let users request access to approved applications through your JSM. Configure granular approval workflows and automatically provision access once approved. Support both SSO and non-SSO applications in one place.
Automate onboarding, role changes, and offboarding
Streamline employee lifecycle management by automating account creation for new hires, department transfers, and departures. Integrations include Active Directory, Azure AD, Okta, Google Workspace, Jumpcloud & others.
Streamline your quarterly access reviews
Run certification campaigns to review who has access to what. Let managers and application owners review access directly in Jira. Automatically revoke access and create audit trails for compliance requirements.
Supporting media
Editions
This app offers two different editions - Standard and Advanced. You can start a free trial of either edition, and change your edition anytime during or after the trial.
Standard
Onboard your team and scale fast
Includes:
Access Requests
Access Reviews
Employee Lifecycle Workflows
Advanced
Unlock the full range of app features
Everything from Standard, plus:
Auto Reclaim Licenses
JSM Virtual Agent Integration
API Access
Audit Logs
Dedicated Slack Support Channel
More details
Multiplier is an identity governance (IGA), access management and least privilege tool built natively for Jira Service Management.
We streamline manual IT processes for access management, orchestration and compliance.
Features
Multiplier helps IT teams automate day-to-day end user requests such as password and MFA resets, access to shared drives and groups, routing approvals to managers etc.
Supported Integrations
- Okta
- Azure AD
- Atlassian (Manage access to Projects/Spaces/Groups)
- Google Workspace
- Jumpcloud
Use Cases
- Self-service access requests in JSM or Slack.
- Enforce just-in-time and time-based access controls.
- Zero touch provisioning and deprovisioning.
- Approval flows (Manager & App Owner) for every app, role, or permission
- Easily generate access reports to see who has been given access to which resource, when and why.
📖 Documentation | 💬 Support | ☎️ Book a demo
Resources
App documentation
Comprehensive set of documentation from the partner on how this app works
Privacy and Security
Privacy policy
Atlassian's privacy policy is not applicable to the use of this app. Please refer to the privacy policy provided by this app's partner.
Partner privacy policySecurity program
This app is part of the Marketplace Bug Bounty program.
About Bug Bounty programIntegration permissions
Multiplier Identity Governance – IGA for Okta & Entra ID integrates with your Atlassian app
Version information
Version 5.3.0•for Jira Cloud
- Release date
- Oct 22nd 2025
- Summary
- Minor version update
- Details
- Minor version update
- Payment model
- Paid via Atlassian
- License type
- Commercial
